Effective Model for CoAP Inspired Trust Aware Scheme in Internet of Things with AES Algorithm
Keywords:
IoT, Security, Security Protocols, AES, Encryption, WAN IoTAbstract
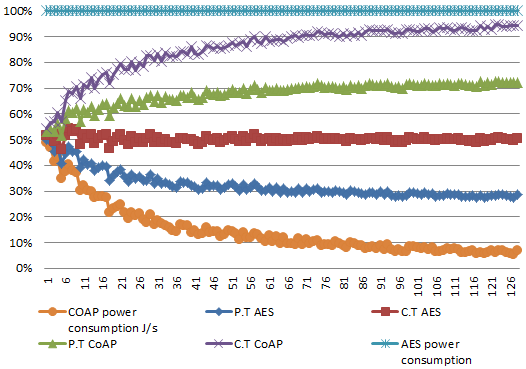
IOT networks have been developed in the realm of technology to make connectivity among the things around us. Networks could only connect computer devices before the Internet of Things (IoT) became a reality. Security is the key issue with these devices. There are significant risks of data loss or hacker assault because these gadgets communicate their data via internet. Challenges from the start have accompanied IoT adoption. In this paper, some of the major difficulties on the way to communicate between gadgets are explored. IoT networks protect user privacy with various types of personal data that are made available for these IoT-based connected devices. To protect IoT-based systems, a trust-aware approach utilizing the CoAP and AES algorithms has been proposed in this paper. The AES method has very robust security, shielding the data and architecture in comparison to others. The utilization of AES coupled with CoAP will enhance the efficacy of the system.
References
E. Akanksha, “Efficient framework to secure communication in IoT using novel finite field encryption,” Adv. Intell. Syst. Comput., vol. 860, pp. 1–11, 2019, doi: 10.1007/978-3-030-00184-1_1/COVER.
K. Zhao and L. Ge, “A survey on the IoT security,” Proc. - 9th Int. Conf. Comput. Intell. Secure. CIS 2013, pp. 663–667, 2013, doi: 10.1109/CIS.2013.145.
M. Dabbagh and A. Rayes, “IoT Security and Privacy,” Internet Things from Hype to Real. Road to Digit. Second Ed., pp. 211–238, Jan. 2018, doi: 10.1007/978-3-319-99516-8_8/COVER.
M. Abdur, S. Habib, M. Ali, and S. Ullah, “Security Issues in the IoT (IoT): A Comprehensive Study,” Int. J. Adv. Comput. Sci. Appl., vol. 8, no. 6, 2017, doi: 10.14569/IJACSA.2017.080650.
H. Beenish and M. Fahad, “5G a review on existing technologies,” 2019 2nd Int. Conf. Comput. Math. Eng. Technol. iCoMET 2019, Mar. 2019, doi 10.1109/ICOMET.2019.8673407.
P. Sethi and S. R. Sarangi, “IoT: Architectures, Protocols, and Applications,” J. Electr. Comput. Eng., vol. 2017, 2017, doi: 10.1155/2017/9324035.
S. Sicari, A. Rizzardi, and A. Coen-Porisini, “Security&privacy issues and challenges in NoSQL databases,” Comput. Networks, vol. 206, p. 108828, Apr. 2022, doi: 10.1016/J.COMNET.2022.108828.
S. Deshmukh and S. S. Sonavane, “Security protocols for IoT: A survey,” 2017 Int. Conf. Nextgen Electron. Technol. Silicon to Software, ICNETS2 2017, pp. 71–74, Oct. 2017, doi: 10.1109/ICNETS2.2017.8067900.
S. Pirbhulal et al., “A Novel Secure IoT-Based Smart Home Automation System Using a Wireless Sensor Network,” Sensors 2017, Vol. 17, Page 69, vol. 17, no. 1, p. 69, Dec. 2016, doi: 10.3390/S17010069.
S. GÖRMÜŞ, H. AYDIN, and G. ULUTAŞ, “Security for the IoT: a survey of existing mechanisms, protocols and open research issues,” J. Fac. Eng. Archit. GAZI Univ., vol. 33, no. 4, pp. 1247–1272, Dec. 2018, doi: 10.17341/GAZIMMFD.416406.
K. Chen et al., “Internet-of-Things Security and Vulnerabilities: Taxonomy, Challenges, and Practice,” J. Hardw. Syst. Secur. 2018 22, vol. 2, no. 2, pp. 97–110, May 2018, doi: 10.1007/S41635-017-0029-7.
G. Mustafa, R. Ashraf, M. A. Mirza, A. Jamil, and Muhammad, “A review of data security and cryptographic techniques in IoT based devices,” ACM Int. Conf. Proceeding Ser., Jun. 2018, doi: 10.1145/3231053.3231100.
M. Elhoseny, K. Shankar, S. K. Lakshmanaprabu, A. Maseleno, and N. Arunkumar, “Hybrid optimization with cryptography encryption for medical image security in IoT,” Neural Comput. Appl., vol. 32, no. 15, pp. 10979–10993, Aug. 2020, doi: 10.1007/S00521-018-3801-X/METRICS.
S. Sasirekha, S. Swamynathan, and S. Suganya, “An ECC-based algorithm to handle secure communication between heterogeneous IoT devices,” Lect. Notes Electr. Eng., vol. 443, pp. 351–362, 2018, doi: 10.1007/978-981-10-4765-7_37/COVER.
J. J. Barriga A and S. G. Yoo, “Security over smart home automation systems: A survey,” Smart Innov. Syst. Technol., vol. 94, pp. 87–96, 2018, doi: 10.1007/978-3-319-78605-6_7/COVER.
C. Stergiou, K. E. Psannis, B. G. Kim, and B. Gupta, “Secure integration of IoT and Cloud Computing,” Futur. Gener. Comput. Syst., vol. 78, pp. 964–975, Jan. 2018, doi: 10.1016/J.FUTURE.2016.11.031.
D. Halabi, S. Hamdan, and S. Almajali, “Enhance the security in smart home applications based on IOT-CoAP protocol,” 6th Int. Conf. Digit. Information, Networking, Wirel. Commun. DINWC 2018, pp. 81–85, May 2018, doi: 10.1109/DINWC.2018.8357000.
D. e. S. Agha, F. H. Khan, R. Shams, H. H. Rizvi, and F. Qazi, “A Secure Crypto Base Authentication and Communication Suite in Wireless Body Area Network (WBAN) for IoT Applications,” Wirel. Pers. Commun., vol. 103, no. 4, pp. 2877–2890, Dec. 2018, doi: 10.1007/S11277-018-5968-Y/METRICS.
B. Yilmaz and S. Özdemir, “Performance comparison of cryptographic algorithms in IoT,” 26th IEEE Signal Process. Commun. Appl. Conf. SIU 2018, pp. 1–4, Jul. 2018, doi: 10.1109/SIU.2018.8404524.
I. Sultan, B. J. Mir, and M. Tariq Banday, “Analysis and optimization of advanced encryption standard for the IoT,” 2020 7th Int. Conf. Signal Process. Integr. Networks, SPIN 2020, pp. 571–575, Feb. 2020, doi: 10.1109/SPIN48934.2020.9071380.
Published
How to Cite
Issue
Section
License
Copyright (c) 2023 50SEA

This work is licensed under a Creative Commons Attribution 4.0 International License.