Cybersecurity Legislature Challenges and Remedies
Keywords:
cyber security, cyber threats, vulnerability, cyberbullying, cyber-crimeAbstract
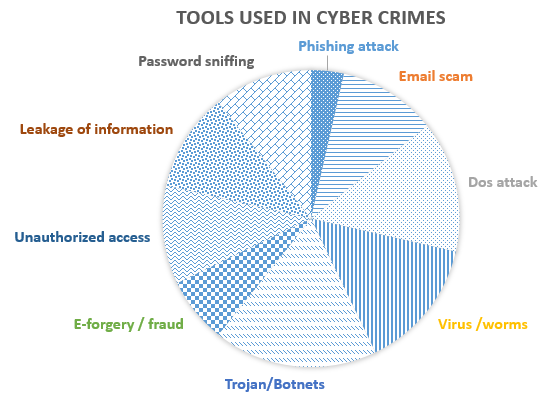
The use of the Internet is growing rapidly in every field of life, such as in business, education, entertainment, information technology, the government sector, and sports. The majority of people are using internet services for online businesses and other online activities. Therefore, it is the need of the hour that the online system should be secure enough, and everyone is fully assured about privacy and the protection of their information. A country needs to have an efficient plan to secure its digital information. Different countries have established legislatures to manage cybercrime activities and cyber threats. In this paper, we analyzed the challenges faced by cybersecurity concerning legislation along with their probable solutions. The purpose of this paper is to provide an extensive review of the literature on cybersecurity, including its loopholes, and present the findings of a survey conducted in various organizations regarding cybersecurity. This study also highlights the improvements and the need for future work in the field of cybersecurity. In addition, the mandatory procedures and mitigation techniques to reduce the occurrence of cybercrime have also been discussed.
References
M. A.-A. M. Al-Amaireh, “The Role of Cybersecurity in Enhancing the Effectiveness of Law Against Cybercrimes,” Rev. Gestão - RGSA, 2024, [Online]. Available: https://rgsa.openaccesspublications.org/rgsa/article/view/6508
L. A. Bygrave, “The emergence of EU cybersecurity law: A tale of lemons, angst, turf, surf and grey boxes,” Comput. Law Secur. Rev., vol. 56, p. 106071, 2025, doi: https://doi.org/10.1016/j.clsr.2024.106071.
B. Badreddine, “National Cybersecurity: A New Evolving Concept,” أبحاث قانونية وسياسية, vol. 10, no. 1, pp. 433–448, 2025, [Online]. Available: https://asjp.cerist.dz/en/article/269649
M. A. Elokaby, “Development of cybersecurity laws in Egypt and its impact on the judicial system (Opportunities and challenges),” Int. Cybersecurity Law Rev. 2024 54, vol. 5, no. 4, pp. 563–584, Oct. 2024, doi: 10.1365/S43439-024-00132-2.
B. S. Mohammad Salem Hamidi, “Designing a Novel Cybersecurity Framework to Prevent Cyber-Attacks with Reference to Least Developing Countries,” Nanotechnol. Perceptions, vol. 20, pp. 159–165, 2024, [Online]. Available: https://www.researchgate.net/publication/382026334_Designing_a_Novel_Cybersecurity_Framework_to_Prevent_Cyber-Attacks_with_Reference_to_Least_Developing_Countries
“Evaluating UK Legislation Effectiveness in Prosecuting Cybercriminals and Deterring Cybercrimes: Identifying Areas for Improvement,” Pakistan J. Criminol., no. 4, pp. 701–721, Sep. 2024, doi: 10.62271/PJC.16.4.701.721.
A. Abisoye and J. I. Akerele, “A Practical Framework for Advancing Cybersecurity, Artificial Intelligence and Technological Ecosystems to Support Regional Economic Development and Innovation,” Int. J. Multidiscip. Res. Growth Eval., vol. 3, no. 1, pp. 700–713, 2022, doi: 10.54660/.IJMRGE.2022.3.1.700-713.
A. Kaminska-Nawrot, D. Bienkowska, and J. Falecki, “A Dignity-Based Approach to Children’s Cybersecurity: A Criminal Analysis,” Eur. Res. Stud. J., vol. XXVIII, no. 1, pp. 3–15, 2025, Accessed: Aug. 21, 2025. [Online]. Available: https://ideas.repec.org/a/ers/journl/vxxviiiy2025i1p3-15.html
M. M. A. Adekunle Emmanuel Makanjuola, “STRENGTHENING CYBERSECURITY IN NIGERIA: A HOLISTIC APPROACH,” Sci. Pract. cyber Secur. J., 2025, [Online]. Available: https://journal.scsa.ge/papers/strengthening-cybersecurity-in-nigeria-a-holistic-approach/
M. W. Hodgins, “The perils of cybersecurity regulation,” Rev. Austrian Econ., 2024, [Online]. Available: https://link.springer.com/article/10.1007/s11138-024-00660-4
D. Neufeld, “Computer crime motives: Do we have it right?,” Sociol. Compass, vol. 17, no. 4, p. 4, 2023, doi: https://doi.org/10.1111/soc4.13077.
C. Nwabachili, “LEGALITY OR OTHERWISE FOR THE IMPOSITION OF CYBER SECURITY LEVY IN NIGERIA,” NAUJILJ, vol. 16, no. 1, 2025, [Online]. Available: file:///C:/Users/VAIO/Desktop/ajol-file-journals_479_articles_295722_682394873c83b.pdf
M. I. Omer Mahmood Watto, “Cyber Law and Cyber Security Policies in Pakistan: A Comparative Study with USA, Canada and Australia,” Pakistan J. Humanit. Soc. Sci., vol. 12, no. 1, 2024, [Online]. Available: https://journals.internationalrasd.org/index.php/pjhss/article/view/1977
I. Elegbe, “CYBERCRIME LEGISLATION: A COMPARATIVE ANALYSIS OF LEGAL FRAMEWORKS, POLICY RESPONSES AND RECOMMENDATIONS,” Int. J. Educ. Soc. Sci. Res., vol. 7, no. 2, 2024, doi: https://doi.org/10.37500/ijessr.2024.7211.
J. Hiller, K. Kisska‐Schulze, and S. Shackelford, “Cybersecurity carrots and sticks,” Am. Bus. Law J., vol. 61, no. 1, pp. 5–29, Mar. 2024, doi: 10.1111/ABLJ.12238’)).
A. R. Mehrdad Falahi, “The Concept of Legislative Criminal Policy in The Blue of Cybercrimes,” Int. J. Adv. Res. Humanit. Law, vol. 1, no. 4, pp. 104–113, 2024, doi: 10.63053/ijrel.36.
K. I. Enver Buçaj, “The need for cybercrime regulation on a global scale by the international law and cyber convention,” Multidiscip. Rev., vol. 8, no. 1, p. 1, 2025, [Online]. Available: https://malque.pub/ojs/index.php/mr/article/view/5348
D. P. K. Shikha Vasishta, “Comparative Trajectories Of Cybersecurity Legislation In Mainland Southeast Asia And China,” Migr. Lett., vol. 21, 2024, [Online]. Available: https://migrationletters.com/index.php/ml/article/view/7768
G. F. A. Waqas Abdullah, “Analyzing China’s Cybersecurity Posture Under Cyber Deterrence Theory: Reshaping Indo-Pacific Security Landscape (2020-2024),” Res. J. Soc. Aff., vol. 3, no. 4, p. 6, 2025, [Online]. Available: https://rjsaonline.com/journals/index.php/rjsa/article/view/265
R. R. Megha Ojha, “Combating Cybercrime: A Study on Problems, Preventions and Cyber Laws of India,” Eur. Econ. Lett., vol. 41, no. 1, 2024, [Online]. Available: https://www.eelet.org.uk/index.php/journal/article/view/1220
L. Qudus, “Cybersecurity governance: Strengthening policy frameworks to address global cybercrime and data privacy challenges,” Int. J. Sci. Res. Arch., vol. 14, no. 1, pp. 1146–1163, Jan. 2025, doi: 10.30574/IJSRA.2025.14.1.0225.
S. N. Othman, A. M. Jawad, R. Hameed, R. T. Kawad, and D. Khlaponin, “The impact of cybersecurity law in the middle east,” Encuentros, no. 23 (enero-abril), pp. 392–420, Jan. 2025, doi: 10.5281/ZENODO.14291287.
Emmanuel Ok, “The Impact of Cybersecurity Laws on Legal Procedures and Case Law,” ResearchGate, 2025, [Online]. Available: https://www.researchgate.net/publication/387625093_The_Impact_of_Cybersecurity_Laws_on_Legal_Procedures_and_Case_Law
O. V. G. Olena Sviatun, “Combating Cybercrime: Economic and Legal Aspects,” WSEAS Trans. Bus. Econ., vol. 18, pp. 751–762, 2021, doi: 10.37394/23207.2021.18.72.
E. C. and R. Mcardle, “The Evolution of Cybercrime and Cyberdefense,” Trend Micro, 2018, [Online]. Available: https://documents.trendmicro.com/assets/white_papers/wp-evolution-of-cybercrime-and-cyberdefense.pdf
S. T. L. Robert W. Gehl, “Social Engineering: How Crowdmasters, Phreaks, Hackers, and Trolls Created a New Form of Manipulative Communication,” MIT Press, 2022, doi: https://doi.org/10.7551/mitpress/12984.001.0001.
B. Wible, “A site where hackers are welcome: Using hack-in contests to shape preferences and deter computer crime,” Yale Law J., vol. 112, no. 6, pp. 1577–1624, 2003, doi: 10.2307/3657453.
A. I. A.-A. Sara Al-Bassam, “The Significance of Cybersecurity System in Helping Managing Risk in Banking and Financial Sector,” J. Xidian Univ., vol. 14, no. 7, 2020, [Online]. Available: https://www.researchgate.net/publication/337086201_The_Significance_of_Cybersecurity_System_in_Helping_Managing_Risk_in_Banking_and_Financial_Sector
M. J. Ali, “Cybercrime and Cybersecurity: A Critical Analysis of Legal Frameworks and Enforcement Mechanisms,” Bharati Int. J. Multidiscip. Res. Dev., vol. 2, no. 8, pp. 137–154, Oct. 2024, doi: 10.70798/BIJMRD/020800017.
M. M. and S. Erickson, “Changing Today’s Law Enforcement Culture to Face 21st-Century Threats,” Herit. Found., 2011, [Online]. Available: https://www.heritage.org/homeland-security/report/changing-todays-law-enforcement-culture-face-21st-century-threats
Guedouari Fatma Zohra . Allouache Mehdi, “The Role Of Cybersecurity In Combating Cybercrime In Algeria: Prospects And Challenges,” Rev. Sci. Hum., vol. 36, no. 2, pp. 347–358, 2025, [Online]. Available: https://asjp.cerist.dz/en/article/273427
J. M. Inês Sousa Guedes, “Explaining fear of cybercrime: A focus on interpersonal and property cybercrime differences,” Eur. J. Criminol., vol. 22, no. 4, 2025, doi: https://doi.org/10.1177/14773708241312820.
N. Z. H. Chee Lee Chong, “Secure File Sharing System with Strong Password and One Time Password Authentication,” J. Comput. Res. Innov., vol. 10, no. 1, p. 3, 2025, doi: https://doi.org/10.24191/jcrinn.v10i1.500.
D. K. Sunitha Prabhu, “Beyond the direct impact of sanctions and subjective norms in cybersecurity,” Inf. Comput. Secur., 2025, doi: 10.1108/ICS-04-2025-0148.
and M. Q. O. Issn, S. Gul, W. Malik, Gohar, “Cybersecurity and sovereignty: the role of international law in governing state behavior in cyberspace,” Policy J. Soc. Sci. Rev., 2025, [Online]. Available: https://www.researchgate.net/publication/392373086_cybersecurity_and_sovereignty_the_role_of_international_law_in_governing_state_behavior_in_cyberspace
A. N.-F. Anant Kumar Verma, “Realigning Academic Cybersecurity Research With Industrial Needs in Cyber-Physical Systems,” IEEE Open J. Ind. Electron. Soc., vol. 99, pp. 1–9, 2025, doi: 10.1109/OJIES.2025.3593689.
M. Grimland et al., “Cyberbullying Victimization and Suicide Attempt Among Adolescents: A Cross-National Comparison,” Int. J. Environ. Res. Public Health, vol. 22, no. 3, Mar. 2025, doi: 10.3390/IJERPH22030385,.
and S. M. F. Julie M. Haney, Clyburn Cunningham IV, “Towards Bridging the Research-Practice Gap: Understanding Researcher-Practitioner Interactions and Challenges in Human-Centered Cybersecurity,” Natl. Inst. Stand. Technol., 2024, [Online]. Available: http://usenix.org/conference/soups2024/presentation/haney
A. N.-F. Anant Kumar Verma, “International Journal for Conventional and Non-Conventional Warfare Cybersecurity and Islamic Law: Navigating the Challenges of the Digital Age,” IEEE Open J. Ind. Electron. Soc., vol. 99, pp. 1–39, 2025, doi: 10.1109/OJIES.2025.3593689.
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2025 50sea

This work is licensed under a Creative Commons Attribution 4.0 International License.